In this tutorial, we will discover a feature built into Windows: auditing access to files and folders.
This feature allows you to log all successful or failed access attempts to shared system resources, such as files or directories.
It is based on a mechanism for logging security events, which can be viewed in the Windows event log.
Enabling auditing on sensitive company files can be essential for detecting abnormal behavior, identifying users behind access, and strengthening overall infrastructure security.
Table of contents
Configuring File and Folder Access Logging
The configuration is done in two steps:
- Enable audit settings on the folder(s) where you want to have access traces
- Configure Audit Policy on Windows Server
Audit configuration on the folder
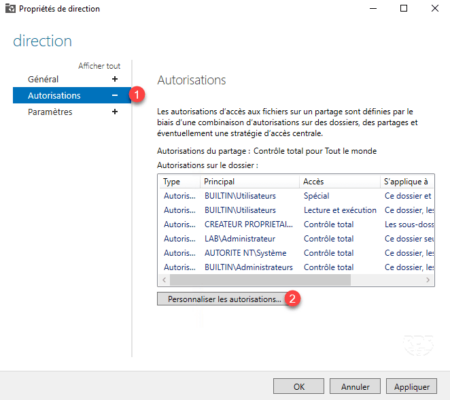
On the file server, open the Share Properties through Server Manager, go to Permissions 1 and then click Customize Permissions 2.
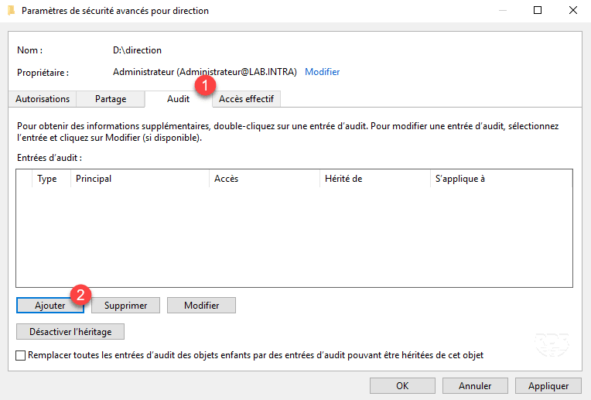
Go to the Audit tab 1 and click Add 2.
Select the users to audit 1, the type (Pass, Fail or All) 2, check the items to record 3 then click OK 4.
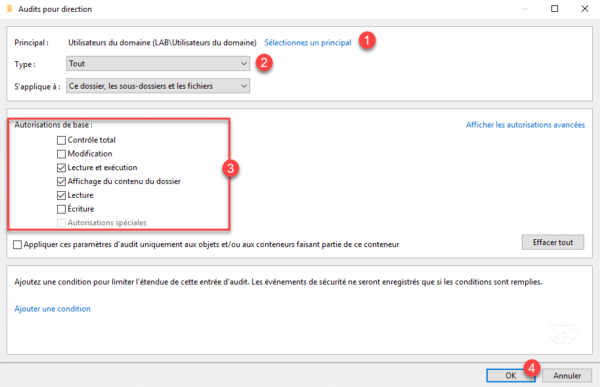
To view all available permissions, including deletions, click Show Advanced Permissions.
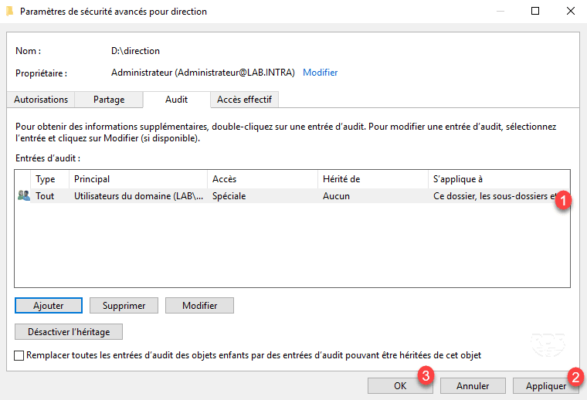
Audit is added 1 and visible as an NTFS permission., click on Apply 2 then OK 3 and close the share properties window.
Configure audit policy on the server
To work, it is necessary to enable object access auditing on the server.
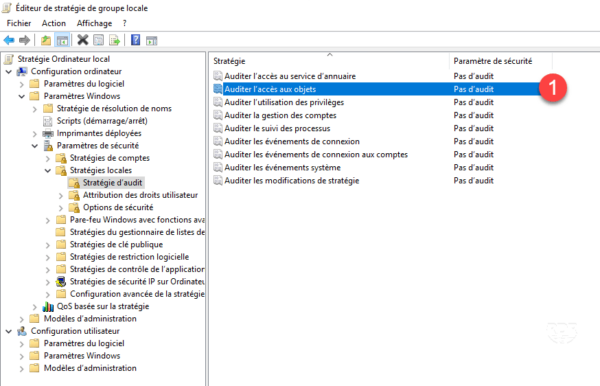
Open a Run window (crtl+R) and enter gpedit.msc to access the computer’s local policy console.
Edit the Audit object access 1 setting located in the following location: Computer Configuration / Windows Settings / Security Settings / Local Policies / Audit Policy.
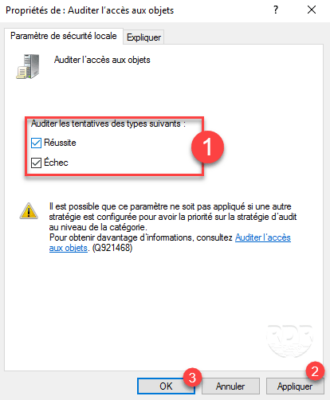
Configure the audit types to be enabled 1 and click Apply 2 then OK 3.
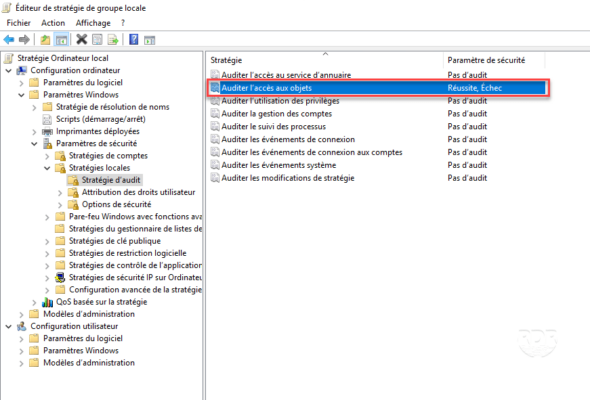
The strategy is configured.
Force a policy update by opening a command prompt as an administrator and running the gpupdate command.
View Windows Logs in Event Viewer
In order to generate logs, access folders and files according to the defined audit parameters.
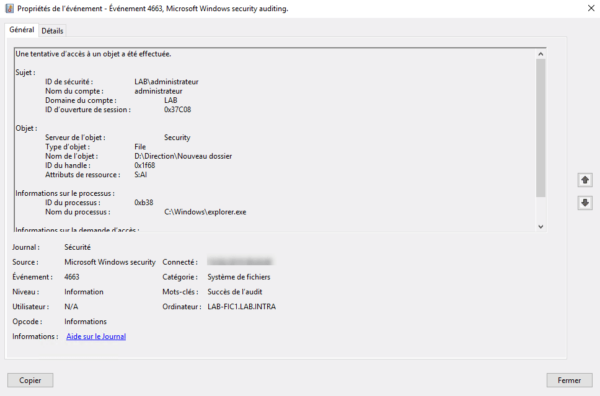
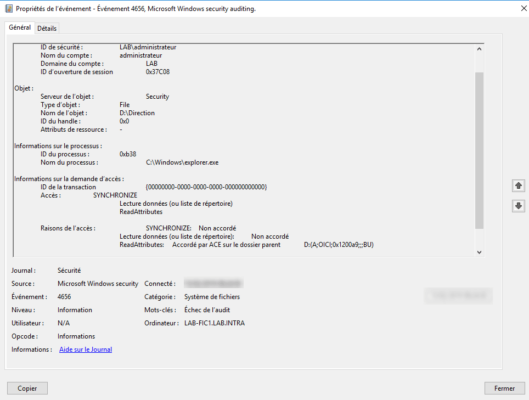
On the server, open the Event Viewer and go to Windows Logs 1 / Security 2. Look for events in the File Systems category.
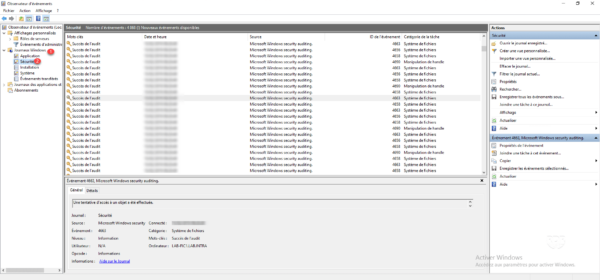
Example of logs:
Conclusion
With auditing features, you can now see users who are browsing shares and being too nosy.
Personally, I advise you to activate this feature on sensitive files and only record refusals, because the number of records can quickly become significant and also impact system performance.
It is also possible to send events to a log well (SIEM) like ELK or Wazuh for easier exploitation.
To best secure access to shares, I also recommend enabling access-based enumeration.
It is also possible to see in real time the files being accessed on a network share.
