Table of Contents
Introduction
In this tutorial, we will see how to secure emails with a Sophos XG firewall.
The firewall offers two modes of operation for filtering emails:
- MTA : the firewall will act as an SMTP relay
- Legacy : it will be placed in transparent mode, which we will see in this tutorial.
In both modes the security options are the same:
- Antivirus filtering
- Antispam filtering with possible quarantine
- Filtering rules.
In the tutorial, we will take a tour of the various protection options available, the Sophos site offers a complete documentation of each available element.
Prerequisites
- Your sophos license must include email protection.
- Mail servers must have been added to the hosts.
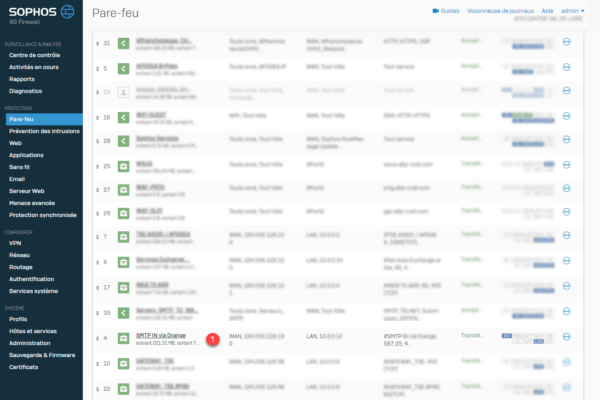
Add a rule for incoming emails
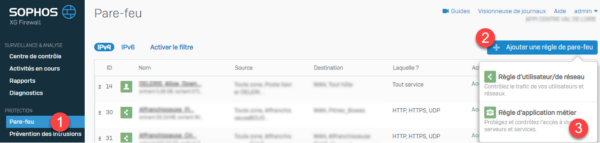
1. On the Web interface go to the list of rules (Firewall) 1 then click Add firewall rule 2 and choose Business application rule 3 .
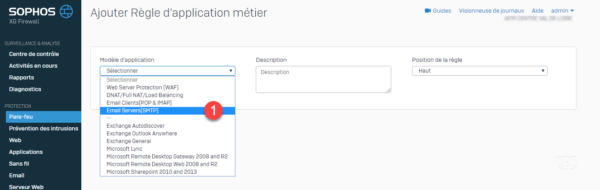
2. In Application Template choose Email Servers (SMTP) 1 .
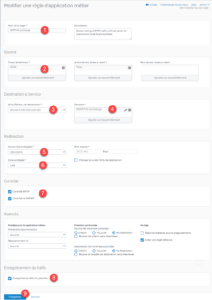
3. Configure the rule:
4. The rule is added 1 .
Configure email protection
The protection of emails is accessible through the menu by clicking on Email.
General Settings
In this part is the general configuration of the SMTP security behavior.
I’m only going to introduce the modules that are used in the LEGACY mode
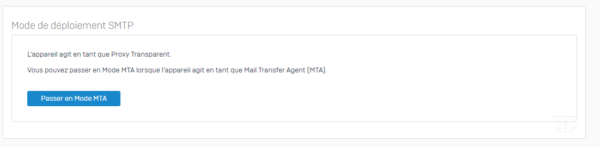
SMTP deployment mode
Change the function mode of SMTP MTA or LEGACY protection.
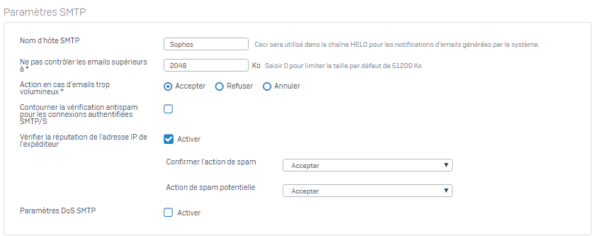
SMTP settings
Adjusts the behavior for scanning attachments and enables reputation control and behavior.
Messaging journal
This option allows you to configure sending incoming copy of email to another mailbox.
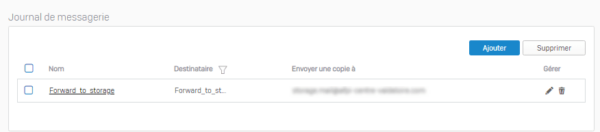
I personally use this option to transfer messages from person leaving the company to the replacement. This will remove the box on the mail server.
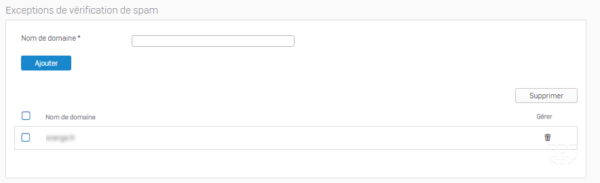
Spam verification exceptions
Allows you to configure domains that will not be scanned by the antispam engine.
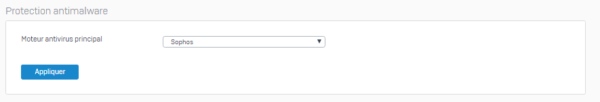
Anti-malware protection
Allows you to choose the antivirus engine (sophos or avira).
Strategies
This section contains the control rules that incoming emails will undergo to know if they are sent to the mail server, quarantined or blocked.
They work like firewall rules, they are read from top to bottom. If an email is not filtered by any of the rules, then it is forwarded to the server.
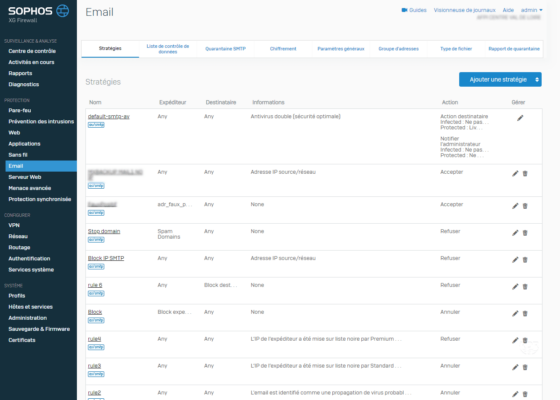
When adding a strategy, there are two choices
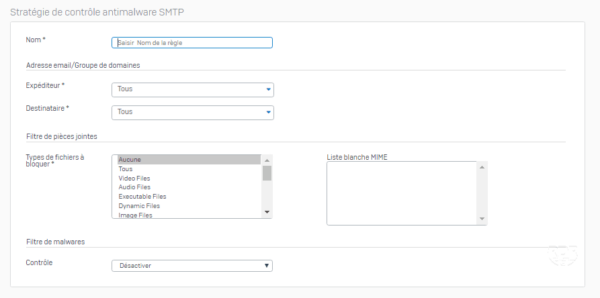
SMTP antimalware control
This control adjusts the antivirus behavior (single / double) depending on the type of attachment.
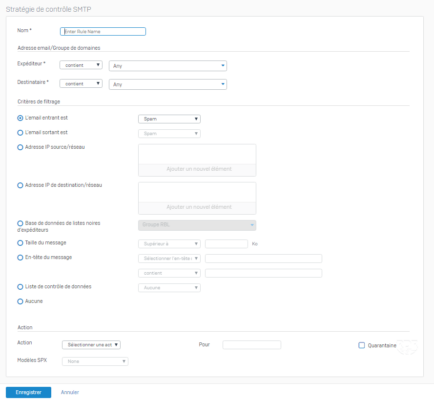
SMTP antispam control
This control makes it possible to configure the behavior of the antispam according to several criteria and to choose an action.
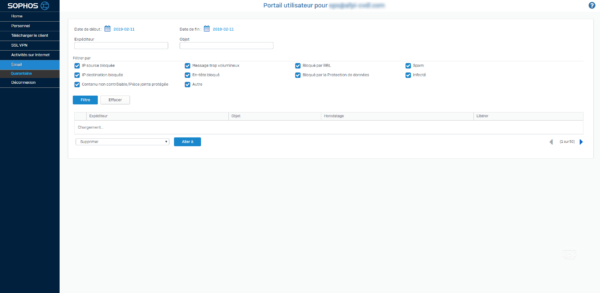
Quarantine report
This option allows you to set the email alerts sent to users if emails are quarantined on the firewall.
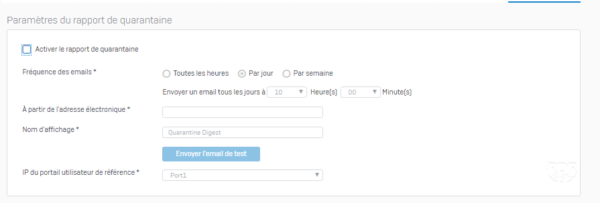
Access to quarantine is not the user portal.