Configure ISATAP to access clients
As we have seen, the DirectAccess connection uses IPv6 and at the moment it is impossible for computers and servers in the corporate network to access clients outside the network.
If you want to access from the inside to the outside, that is to the connected customers, you have to configure an IPv6 gateway, it can be convenient for the support teams to take control of a computer.
The ISATAP gateway will be the DirectAccess server, there are several ways to configure this gateway, in this tutorial we will see how to do it in PowerShell.
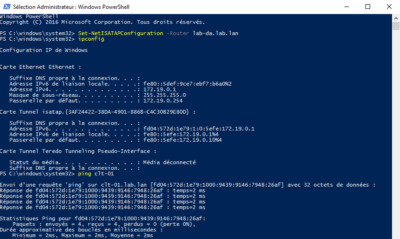
Open a PowerShell command prompt as an administrator and enter:
Set-NetISATAPConfiguration -Router <fqdn.server-directaccess.lan>The screenshot below shows the command above, then an ipconfig and a ping to the client connected by DirectAccess.